26/04/2020
In an era where hailing a cab is often done with a tap on a smartphone and payments are seamlessly cashless, the taxi industry has undergone a profound digital transformation. This evolution has brought unparalleled convenience and efficiency, but it has also introduced a new frontier of challenges: cybersecurity. While the everyday driver or taxi operator might not directly interact with complex cyber threat intelligence standards, understanding their importance is crucial. These sophisticated frameworks, such as STIX 2 and TAXII 2, are silently working behind the scenes, fortifying the digital infrastructure that underpins modern transport, including the very taxi services we rely upon daily.
Consider the myriad of digital touchpoints in a typical taxi journey today: booking apps, GPS navigation, cashless payment systems, and sophisticated dispatch software. Each of these represents a potential vulnerability if not adequately protected. A cyber-attack isn't just a distant threat for large corporations; it can paralyse a taxi fleet, compromise sensitive customer data, or even disrupt an entire city's transport network. This is where the world of cyber threat intelligence, guided by standards like STIX 2 and TAXII 2, becomes incredibly relevant, even for the seemingly traditional taxi business.
- What Are STIX 2 and TAXII 2? The Digital Defenders Explained
- Why These Standards Matter for the UK Taxi Industry
- How Threat Intelligence Works: A Comparison
- Using the Standards: A Look Under the Bonnet
- The Role of Government and Wider Adoption
- Beyond the Standards: Continuous Vigilance
- Frequently Asked Questions for Taxi Operators
- The Journey Ahead: A Secure Digital Highway
What Are STIX 2 and TAXII 2? The Digital Defenders Explained
At their core, STIX 2 and TAXII 2 are open standards designed to enhance the sharing and understanding of cyber threat intelligence. Think of them as a universal language and a standardised delivery system for information about digital dangers. They allow different security systems and organisations to communicate efficiently and effectively about emerging threats, rather than operating in isolated silos.
STIX 2 (Structured Threat Information Expression) provides a standardised, machine-readable format for describing cyber threat information. Before STIX 2, intelligence might have been shared in various disparate formats, making it difficult for automated systems to process and understand. STIX 2 organises this information in a repeatable way, making it comprehensible to both human analysts and machines. This includes details about attack patterns, malware, vulnerabilities, and the tactics used by threat actors.
TAXII 2 (Trusted Automated eXchange of Indicator Information) acts as the secure, automated conduit for exchanging this STIX-formatted intelligence. If STIX 2 is the language, TAXII 2 is the postman, ensuring that the intelligence reaches the right recipients quickly and securely. It enables machine-to-machine automated information exchange, drastically speeding up the time it takes for security systems to receive and act upon new threat information.
While a local taxi firm won't be implementing these standards directly, the security solutions they use – from their payment processors to their cloud-based dispatch systems – are increasingly benefiting from the intelligence shared via these protocols. Moreover, government bodies and national cybersecurity centres, which protect critical national infrastructure (including transport), extensively use these standards to create a safer digital environment for everyone.
Why These Standards Matter for the UK Taxi Industry
The direct application of STIX 2 and TAXII 2 might seem far removed from the daily operations of a taxi company. However, their indirect benefits are profound and directly impact the security, reputation, and operational continuity of every digital-first taxi service.
1. Enhanced Data Protection and Compliance
Modern taxi services collect and process a wealth of sensitive data: customer names, contact details, payment information, journey histories, and even real-time location data. Breaches of this information can lead to severe financial penalties under regulations like GDPR, significant reputational damage, and a loss of customer trust. STIX 2 and TAXII 2 help the broader cybersecurity ecosystem to identify and disseminate information about new threats more quickly. This means that the security products and services used by taxi companies (or their third-party providers) are updated faster to defend against emerging attack vectors, ultimately protecting valuable customer data.
2. Safeguarding Operational Resilience
Imagine a scenario where a ransomware attack encrypts a taxi company's dispatch system, or a denial-of-service attack takes down their booking app. The result would be immediate operational paralysis, lost revenue, and frustrated customers. By enabling faster, more efficient sharing of threat intelligence, STIX 2 and TAXII 2 contribute to a more robust global defence against such attacks. This means that if a new type of ransomware targeting transport systems emerges, intelligence about it can be rapidly shared, allowing security vendors to develop and deploy countermeasures before it impacts widespread operations. This contributes directly to the operational resilience of the taxi sector.
3. Speeding Up Threat Response
The speed at which cyber threats evolve demands an equally swift response. Manual processes for sharing and interpreting threat intelligence are simply too slow. The machine-readable format of STIX 2 and the automated exchange capabilities of TAXII 2 dramatically reduce human intervention, allowing for near real-time updates to security systems. This rapid dissemination of intelligence means that defences can be updated within minutes, rather than hours or days, significantly reducing the window of vulnerability for potential attacks on digital infrastructure, including that used by taxi services.
4. Identifying Attack Origins and Patterns
A key benefit of these standards is their ability to link indicators of compromise (evidence of an attack) to tactics, techniques, and procedures (how threat actors operate). For example, if a specific phishing campaign targets transport companies, STIX 2 can describe the characteristics of that campaign, and TAXII 2 can share it. This allows security analysts (at a government level or within large security firms) to identify the source of attacks, understand the methods used, and predict future threats. While a taxi firm won't be doing this analysis themselves, they benefit from a more informed and proactive defence strategy deployed by the entities protecting the wider digital infrastructure they rely upon.
How Threat Intelligence Works: A Comparison
To further illustrate the benefits, let's compare how threat intelligence might have been shared in the past versus the modern, standardised approach enabled by STIX 2 and TAXII 2:
| Feature | Traditional/Manual Threat Intelligence | STIX 2 & TAXII 2 Enabled Intelligence |
|---|---|---|
| Format | Varied documents (PDFs, emails, spreadsheets), often unstructured. | Standardised, machine-readable JSON format. |
| Sharing Method | Emails, phone calls, in-person meetings, secure portals (often manual uploads). | Automated, machine-to-machine exchange via RESTful API over HTTPS (TAXII 2). |
| Speed of Exchange | Slow; dependent on human intervention, leading to delays. | Rapid, near real-time; intelligence can be disseminated globally in minutes. |
| Actionability | Requires manual parsing and interpretation by analysts; prone to human error. | Directly consumable by security tools and systems for automated defence updates. |
| Consistency | Inconsistent terminology and definitions across different sources. | Consistent, defined objects and relationships (e.g., Attack Patterns, Malware). |
| Global Reach | Limited to direct relationships and manual distribution. | Facilitates widespread, automated sharing among diverse organisations globally. |
| Effort Required | High manual administration for creating, distributing, and consuming intelligence. | Significantly reduced manual overhead; more focus on analysis and response. |
Using the Standards: A Look Under the Bonnet
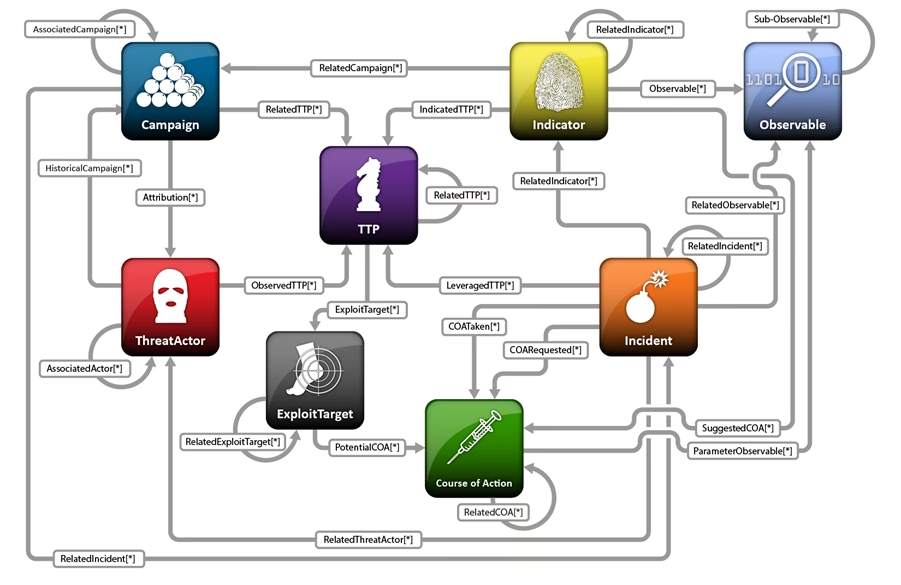
For those interested in the technicalities, or for taxi companies engaging with cybersecurity providers, understanding the components of STIX 2 and TAXII 2 is insightful. STIX 2 defines 12 core 'Domain Objects' that describe various aspects of cyber threats. These include:
- Attack Patterns: Reusable descriptions of how adversaries try to achieve their objectives.
- Campaigns: A set of malicious behaviours or attacks that are related to a common goal.
- Course of Action: Recommended responses or mitigations to a threat.
- Identity: Information about a person, organisation, or group involved in threat intelligence.
- Indicator: A pattern of suspicious activity that can be used to detect threats.
- Intrusion Set: A grouped set of adversarial behaviours and resources with a common intent.
- Malware: Malicious software.
- Observed Data: Concrete instances of data observed on a system or network.
- Report: A collection of threat intelligence focused on a specific topic.
- Threat Actor: An individual or group that is an adversary.
- Tool: Legitimate software that can be used by adversaries.
- Vulnerability: A weakness in a system or software.
When intelligence is shared using TAXII 2, it typically involves a 'TAXII Collection', which is a logical grouping of cyber threat intelligence. Organisations can subscribe to these collections, effectively signing up to receive specific types of threat updates. This publish-subscribe model ensures that relevant intelligence reaches the right user groups efficiently.
The emphasis on machine-to-machine exchange using a RESTful API over HTTPS ensures that the intelligence is not only timely but also securely transmitted. This level of automation is crucial in today's fast-paced threat landscape, allowing for rapid deployment of countermeasures and continuous adaptation of security postures.
The Role of Government and Wider Adoption
The UK government plays a significant role in promoting and adopting these standards, particularly through its open standards approval process. This commitment underscores the strategic importance of standardised threat intelligence for national security and economic resilience. When the government, alongside other international partners and leading security technology suppliers, embraces these standards, it creates a powerful network effect. The wider the adoption, the easier it becomes for diverse entities to share and act upon analysis of threat intelligence, creating a more secure digital environment for all sectors, including transport.
For the taxi industry, this widespread adoption means that the security tools and services they procure are more likely to be integrated into this global intelligence network. It means that the threats identified by a government agency in one country can be rapidly communicated to security systems protecting a taxi fleet in the UK, leading to a more proactive and robust defence.
Beyond the Standards: Continuous Vigilance
While STIX 2 and TAXII 2 significantly increase levels of automation in threat intelligence, it's crucial to remember that they are tools to augment, not replace, human expertise. Full automation without human oversight risks creating unintended consequences, such as a self-inflicted denial of service. Therefore, training users on how to effectively utilise and interpret the intelligence shared through these standards remains paramount. For taxi companies, this translates to ensuring that their IT personnel or outsourced IT providers are well-versed in modern cybersecurity practices and can leverage the benefits of this global intelligence sharing.
Frequently Asked Questions for Taxi Operators
Q: Do I need to implement STIX 2 and TAXII 2 in my taxi company?
A: No, typically not directly. These standards are primarily used by government agencies, large enterprises, and cybersecurity vendors to share and consume threat intelligence at a high level. However, the security products and services you use (e.g., cloud providers, payment systems, security software) benefit from this intelligence, making your operations safer.
Q: How does this protect my customers' data?
A: By enabling faster and more accurate sharing of cyber threat information, these standards help the broader cybersecurity community detect and respond to new threats more quickly. This means the systems that store your customer data are better protected against the latest malware, phishing attacks, and data breaches, reducing the risk of a compromise.
Q: What are the biggest cyber threats to a taxi business?
A: Key threats include ransomware (locking up dispatch or payment systems), data breaches (exposing customer or driver information), phishing attacks (tricking employees into revealing credentials), and denial-of-service attacks (making your booking apps or website unavailable). GPS spoofing or tampering with vehicle systems could also be emerging concerns.
Q: What can a small taxi company do to improve its cybersecurity?
A: Focus on strong basics: regular software updates, robust password policies, multi-factor authentication, employee cybersecurity awareness training, regular data backups, and using reputable security software. Consider engaging a cybersecurity consultant to assess your specific risks and ensure compliance with data protection regulations.
Q: Is cybersecurity an ongoing concern, or a one-time fix?
A: Cybersecurity is an ongoing process, not a one-time fix. The threat landscape is constantly evolving, with new vulnerabilities and attack methods emerging daily. Continuous monitoring, regular updates, and staying informed about best practices are essential to maintain a strong security posture.
The Journey Ahead: A Secure Digital Highway
The digital transformation of the taxi industry is irreversible, bringing immense benefits alongside new responsibilities. While the intricate workings of STIX 2 and TAXII 2 might reside in the realm of high-level cybersecurity, their impact reverberates through every connected sector, including urban transport. For UK taxi services, understanding that a robust, collaborative cybersecurity ecosystem is actively working to protect the digital highways they operate on is key. By embracing modern security practices and partnering with providers who leverage cutting-edge threat intelligence, taxi companies can ensure that their journeys remain safe, secure, and uninterrupted, protecting both their operations and their valued passengers.
If you want to read more articles similar to Shielding the Ride: Cybersecurity for Taxis, you can visit the Taxis category.

