26/12/2016
In the evolving landscape of cyber threats, staying one step ahead is paramount. For many organisations, especially those operating with limited resources, acquiring and integrating robust threat intelligence can feel like an insurmountable challenge. You’re not alone if you've found yourself pondering how to effectively ingest valuable Indicators of Compromise (IOCs) into your security information and event management (SIEM) solution, particularly when commercial feeds are out of reach. This article delves into how Microsoft Sentinel, a scalable, cloud-native SIEM and security orchestration, automation, and response (SOAR) solution, can be leveraged to consume threat intelligence from TAXII servers and other sources, even exploring options for free feeds.

- Understanding STIX and TAXII for Threat Intelligence
- Microsoft Sentinel's Threat Intelligence Capabilities
- Sourcing Free STIX/TAXII Feeds for Sentinel
- Practical Steps for Threat Intelligence Ingestion
- Maximising Your Threat Intelligence
- Comparative Table: Ingestion Methods
- Frequently Asked Questions (FAQs)
- Q: Is Anomali Limo still a viable free STIX/TAXII feed for Microsoft Sentinel?
- Q: Are there many truly free, high-quality STIX/TAXII threat intelligence feeds available?
- Q: Can I use other formats besides STIX, CSV, or JSON for threat intelligence in Sentinel?
- Q: What's the main benefit of using the TAXII connector over manual uploads?
- Q: How do I ensure my threat intelligence is always current in Sentinel?
- Conclusion
Understanding STIX and TAXII for Threat Intelligence
Before diving into the specifics of Microsoft Sentinel, it’s crucial to grasp the foundational concepts of STIX and TAXII. These are not just buzzwords; they are the bedrock of standardised threat intelligence sharing.
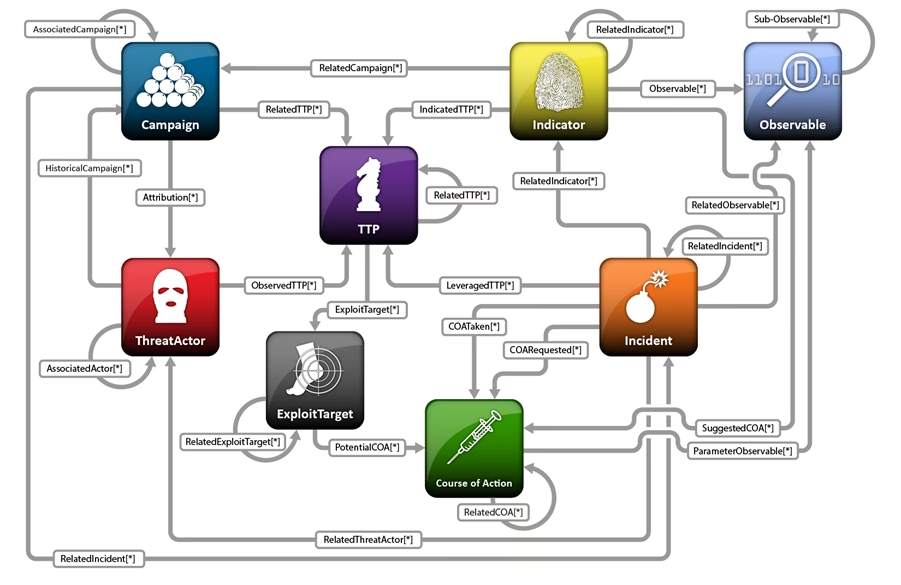
What is STIX?
STIX, or the Structured Threat Information eXpression, is a standardised language for conveying cyber threat information. Think of it as a common vocabulary that allows different security tools and organisations to understand and process threat data consistently. STIX defines a wide range of cyber observables, attack patterns, malware, campaigns, and more, providing a comprehensive framework for describing threats. Its structured nature makes it machine-readable, enabling automated processing and analysis. For instance, an IOC describing a malicious IP address or a specific file hash would be represented in a structured STIX format, making it easily consumable by security platforms.
What is TAXII?
While STIX provides the 'what' of threat intelligence, TAXII, or the Trusted Automated eXchange of Indicator Information, provides the 'how'. TAXII is a set of services and message exchanges that enable automated sharing of STIX-formatted threat intelligence. It acts as a transport mechanism, allowing organisations to subscribe to threat intelligence feeds from various providers. Imagine it as the delivery service for your threat intelligence parcels. TAXII servers publish threat intelligence, and clients can request and receive this information in a standardised, automated way. This automation is key for keeping your threat intelligence up-to-date without constant manual intervention.
Microsoft Sentinel's Threat Intelligence Capabilities
Microsoft Sentinel is designed with threat intelligence integration at its core. It offers multiple pathways to ingest and utilise threat data, ensuring you can bring in IOCs from various sources and formats. This flexibility is particularly beneficial when working with budget constraints, as it allows for both automated, real-time feeds and more manual, ad-hoc uploads.
Native TAXII Connector in Sentinel
Yes, Microsoft Sentinel can indeed ingest data directly from TAXII servers. Sentinel provides a built-in data connector specifically designed for TAXII feeds. This native integration simplifies the process of subscribing to and receiving threat intelligence published via TAXII. When configured, Sentinel acts as a TAXII client, pulling STIX-formatted data from the specified TAXII server. This method is highly recommended for its automation and the ability to keep your threat intelligence continuously updated. It eliminates the need for scripting or complex parsing, as Sentinel handles the STIX structure natively.
Custom Feeds via Upload (CSV/JSON)
Beyond the native TAXII connector, Sentinel offers robust capabilities for ingesting threat intelligence through manual or semi-automated uploads. If you have threat intelligence in CSV or JSON format, you can upload it directly through the Threat Intelligence page within Sentinel. This is particularly useful for one-off imports, data from sources that don't offer TAXII feeds, or for smaller, curated lists of IOCs. When uploading, you'll be guided through a mapping process to ensure the data aligns with Sentinel's schema. This flexibility means that even if a desired free feed isn't available via TAXII, you might still be able to utilise it if it offers downloadable data in a compatible format.
The ThreatIntelligenceIndicator Table
Regardless of the ingestion method – be it via the native TAXII connector, manual upload, or even through other data connectors like Log Analytics API or custom solutions – all threat intelligence in Microsoft Sentinel converges into a unified table: ThreatIntelligenceIndicator. This table is the central repository for all your IOCs. Once indicators are in this table, they become actionable. You can then query them using Kusto Query Language (KQL) to hunt for threats, create analytics rules to trigger alerts based on matches with your log data, and even build workbooks for visualising your threat landscape. Understanding this table is crucial for leveraging your ingested threat intelligence effectively.
Sourcing Free STIX/TAXII Feeds for Sentinel
The quest for free, high-quality, and consistently updated STIX/TAXII threat intelligence feeds is a common one, especially when operating on a tight budget. As you've experienced with Anomali Limo, which appears to be outdated, truly enterprise-grade free feeds that are actively maintained can be challenging to find. Most commercial threat intelligence vendors offer paid subscriptions for comprehensive, real-time data.
However, there are avenues to explore, though they may require more effort in curation and validation:
- Open-Source and Community Feeds: Various open-source projects and cybersecurity communities share threat intelligence. These might not always be in a direct STIX/TAXII format but could offer data in CSV or JSON that you can then upload. Examples often include lists of malicious IPs, domains, or hashes. Their update frequency and reliability can vary significantly.
- Vendor-Specific Free Tiers/Samples: Some commercial threat intelligence providers might offer a very limited free tier or sample feeds as a taster for their full services. These are typically not comprehensive but can provide a glimpse into their data quality.
- National CERTs/CSIRTs: Some national Computer Emergency Response Teams (CERTs) or Cyber Security Incident Response Teams (CSIRTs) might share threat intelligence with specific communities or the public, sometimes in STIX/TAXII format, though access might be restricted to national entities or specific sectors.
- Academic and Research Initiatives: Universities or research groups sometimes publish threat intelligence data as part of their studies. These are often static datasets but can be valuable for historical analysis or specific threat types.
It's important to set realistic expectations. While free feeds exist, they rarely offer the breadth, depth, and timely updates of commercial alternatives. They often serve as a good starting point or a supplementary source rather than a complete solution for sophisticated threat detection.
Practical Steps for Threat Intelligence Ingestion
Let's outline the practical steps for getting threat intelligence into your Microsoft Sentinel workspace.
Configuring the TAXII Data Connector
To enable the native TAXII connector:
- Navigate to the 'Data connectors' blade in your Microsoft Sentinel workspace.
- Search for 'Threat Intelligence - TAXII'.
- Click 'Open connector page'.
- You'll need the TAXII server's API Root and Collection ID(s). These are typically provided by the threat intelligence feed vendor. For free feeds, this information might be found in their documentation.
- Enter a friendly name for the connector.
- Select the Polling Frequency (e.g., every 1 hour, every 24 hours).
- Click 'Add'. Sentinel will then begin polling the TAXII server for new STIX data and ingest it into your ThreatIntelligenceIndicator table.
Uploading Custom Feeds (CSV/JSON) and Mapping
For data in CSV or JSON formats:
- Go to the 'Threat intelligence' blade in Microsoft Sentinel.
- Click 'Upload indicators'.
- Select the format (CSV or JSON).
- Upload your file.
- The crucial step here is the 'Map fields' section. You'll need to map the columns/fields from your uploaded file to the corresponding fields in the ThreatIntelligenceIndicator table. For example, if your CSV has a column named 'IP_Address', you would map it to the 'NetworkIP' field in Sentinel. Similarly, 'Hash_Value' would map to 'FileHashValue'.
- Ensure you map essential fields like 'IndicatorType', 'Value', and 'Description' to make the indicators actionable and understandable.
- Review and confirm the upload.
This manual upload method requires you to periodically re-upload updated files if the source feed changes, as it's not automated like the TAXII connector.
Maximising Your Threat Intelligence
Having threat intelligence in Sentinel is just the first step. The real value comes from actively using it.
Querying the ThreatIntelligenceIndicator Table
You can directly query the ThreatIntelligenceIndicator table using KQL to gain insights. For example, to see all active IP indicators:
ThreatIntelligenceIndicator | where Active == true | where IndicatorType == "IPv4-Addr" | project Description, NetworkIP, ThreatType, LastReportedDateTimeCreating Analytics Rules
The most powerful use of your ingested threat intelligence is to create analytics rules. These rules automatically compare your ingested logs (e.g., firewall logs, DNS logs, proxy logs) against the IOCs in the ThreatIntelligenceIndicator table. If a match is found, an alert is generated, enabling your security operations centre (SOC) to investigate immediately. Sentinel provides built-in templates for threat intelligence matching rules, or you can create custom ones tailored to your specific log sources and threat types. This proactive monitoring is essential for identifying potential compromises quickly.
Comparative Table: Ingestion Methods
Understanding the pros and cons of each ingestion method can help you choose the best approach for different threat intelligence sources.
| Feature | TAXII Connector | Manual CSV/JSON Upload |
|---|---|---|
| Automation | Fully automated, scheduled polling | Manual upload, requires periodic re-upload for updates |
| Data Format | STIX (natively parsed) | CSV, JSON (requires field mapping) |
| Update Frequency | Configurable (e.g., hourly, daily) | As frequent as manual uploads allow |
| Complexity | Low (once configured) | Moderate (mapping required, ongoing effort for updates) |
| Ideal Use Case | Consistently updated, structured feeds from providers | One-off IOC lists, custom curated data, non-TAXII sources |
| Cost Implications | Typically associated with commercial feeds, but free TAXII servers exist | Free if data is freely available, but requires manual effort |
Frequently Asked Questions (FAQs)
Q: Is Anomali Limo still a viable free STIX/TAXII feed for Microsoft Sentinel?
A: Based on your observation and general community feedback, Anomali Limo appears to be outdated and not actively updated. While it might have served as a demonstration in the past, it's unlikely to provide current, actionable threat intelligence for real-world defence. It's best to look for more actively maintained sources.
Q: Are there many truly free, high-quality STIX/TAXII threat intelligence feeds available?
A: Truly free, high-quality, and continuously updated STIX/TAXII feeds that rival commercial offerings are rare. Most comprehensive feeds come with a cost due to the significant effort involved in collecting, curating, and distributing timely threat intelligence. However, open-source projects, community efforts, and some academic initiatives do provide valuable free data, often requiring more manual effort to ingest and validate.
Q: Can I use other formats besides STIX, CSV, or JSON for threat intelligence in Sentinel?
A: While STIX (via TAXII), CSV, and JSON are the primary native ingestion methods, you can potentially bring in data from other formats by using Azure Functions or Logic Apps to parse and transform the data into a format that Sentinel can ingest (e.g., pushing it to a Log Analytics custom log table or directly into the ThreatIntelligenceIndicator table via API). This requires more technical expertise.
Q: What's the main benefit of using the TAXII connector over manual uploads?
A: The main benefit of the TAXII connector is automation. Once configured, it automatically pulls and updates threat intelligence indicators, ensuring your Sentinel workspace always has the latest IOCs without manual intervention. Manual uploads, while flexible, require ongoing effort to keep the data current.
Q: How do I ensure my threat intelligence is always current in Sentinel?
A: For automated updates, leverage the native TAXII connector with a suitable polling frequency for any available TAXII feeds. For custom feeds, establish a regular schedule for re-uploading updated CSV/JSON files. Consider automating this process using Azure Logic Apps or Functions if the source allows for programmatic access.
Conclusion
Microsoft Sentinel provides a powerful and flexible platform for ingesting and leveraging threat intelligence, making it an invaluable asset for any security team. While the search for truly free, enterprise-grade STIX/TAXII feeds can be challenging, Sentinel's native TAXII connector and robust custom upload capabilities ensure you can utilise whatever threat intelligence sources are available to you, even on a lean budget. By understanding how to ingest data into the ThreatIntelligenceIndicator table and then building effective analytics rules, you can transform raw IOCs into actionable insights, significantly bolstering your organisation's cyber defence posture. Keep exploring, keep experimenting, and keep your Sentinel fed with the latest threat intelligence to stay ahead of the curve.
If you want to read more articles similar to Sentinel & TAXII: Boosting Threat Intelligence, you can visit the Taxis category.
