08/05/2024
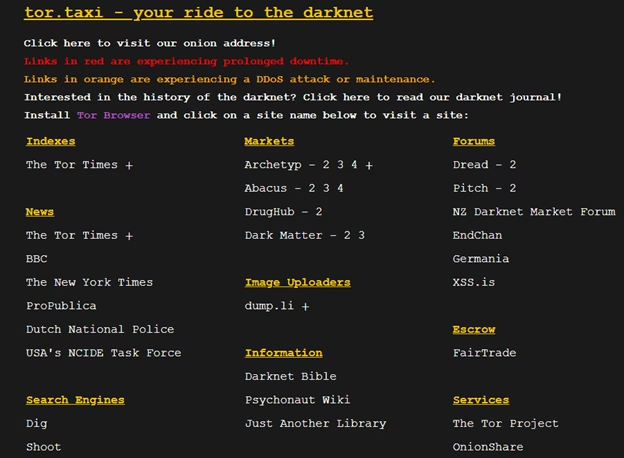
In the evolving landscape of online services, discerning legitimacy can be a challenge, particularly when delving into less conventional corners of the internet. The question 'Is tor.taxi legit?' often arises, prompting a deeper look not just at the service itself, but at the underlying technology that enables such platforms: Tor Browser. While tor.taxi has received a rather low score from some evaluative metrics, indicating a need for caution, it is still widely considered legitimate by its users. The complexities of its operation, often involving onion links or I2P, highlight the unique nature of services operating within the Tor network.
This article will dissect the legitimacy of tor.taxi, explore the fundamental principles of Tor Browser, and provide a comprehensive guide to its functionality, advantages, disadvantages, and crucial safety measures. Understanding Tor is not just about accessing hidden services; it's about comprehending a powerful tool designed for anonymity and freedom in the digital realm.
- Unpacking the Legitimacy of Tor.taxi
- What is Tor Browser and Why is it Used?
- Getting Started with Tor Browser
- How Tor's Anonymity Works: The Layered Approach
- Is Tor Browser Truly Safe? Weighing the Risks
- The Advantages of Using Tor Browser
- The Disadvantages and Dangers of Tor Browser
- Tor vs. VPN: A Critical Comparison
- Essential Tips for Safe Tor Browsing
- Frequently Asked Questions About Tor.taxi and Tor Browser
- Uninstalling Tor Browser: A Simple Process
Unpacking the Legitimacy of Tor.taxi
The immediate answer to 'Is tor.taxi legit?' is nuanced. While some online evaluations assign it a 'pretty low score' and advise caution, user consensus often leans towards its legitimacy. This discrepancy typically arises from the inherent nature of services operating on the dark web or through anonymity networks like Tor. Traditional legitimacy metrics, which rely on clear identification and conventional web structures, may struggle to accurately assess platforms designed specifically to operate outside these norms.
Users frequently attest to the reliability of tor.taxi, often preferring to access it via its onion link or, as is now the case, its I2P link. This shift from onion to I2P signifies an adaptation within the anonymity network landscape. Furthermore, the mention of 'daunt.link', operated by the makers of Dread, suggests a connection to a broader ecosystem of dark web communities and services, which often lend credibility through association within these circles. However, it is paramount for any user to exercise extreme caution. The very nature of anonymous browsing means that while a service might be functional and used by many, the risks associated with the environment it operates within remain high.
What is Tor Browser and Why is it Used?
At the heart of anonymous online interaction, including services like tor.taxi, lies Tor Browser. Tor, an acronym for 'The Onion Router', is a free and open-source web browser designed to enable anonymous communication. It directs internet traffic through a worldwide, volunteer-overlay network consisting of thousands of relays to conceal a user's location and usage from anyone conducting network surveillance or traffic analysis.
The Onion Router Explained
Tor earns its name from the layered encryption process, akin to the layers of an onion. When you use Tor, your data is encrypted multiple times and then sent through a series of volunteer-run servers, known as relays or nodes, across the globe. Each relay decrypts one layer of encryption to reveal the next relay's address, until the final exit node decrypts the outermost layer and sends the unencrypted data to its destination. This multi-layered process ensures that no single relay knows both the origin and the final destination of the data, thereby protecting your identity and browsing activity.
Why Anonymity Matters: Common Uses of Tor
The primary appeal of Tor Browser is its ability to provide anonymity. It effectively hides users from various entities that might monitor online activity, including Internet Service Providers (ISPs), government agencies, advertisers, and cybercriminals. This robust data encryption attracts a diverse range of users, regardless of their specific motivations. Here are some key reasons why individuals choose to install and use Tor Browser:
- Illegal Trading: Unfortunately, Tor can serve as a black market for cybercriminals, facilitating the exchange of illicit goods and services, from hacking expertise to stolen personal data.
- Illegal Materials: Certain Tor sites host content that is restricted or illegal on the clear web, such as copyrighted materials, sensitive government documents, or objectionable imagery.
- Whistleblowing: For individuals exposing misconduct or corruption, Tor provides a critical layer of protection. Edward Snowden famously utilised Tor to safeguard his identity while revealing NSA surveillance programmes.
- Bypassing Censorship: In countries with strict internet censorship, Tor offers a vital lifeline, allowing citizens to access otherwise blocked content and communicate freely without fear of persecution.
- Bypassing Restricted Content: Tor can help users circumvent geo-blocking restrictions imposed by streaming services or websites, allowing access to content unavailable in their geographical region.
- Health Privacy: Many users seek to maintain strict privacy regarding sensitive health information, wishing to conceal it from family members, insurance companies, or other inquisitive parties.
- Journalism: Investigative journalists, particularly those working on sensitive stories, rely on Tor to conduct research and communicate with sources securely, protecting both their identity and that of their informants.
Beyond these specific applications, many individuals use Tor simply for everyday browsing, valuing the enhanced anonymity and privacy it offers over conventional browsers.
Getting Started with Tor Browser
Accessing Tor Browser is relatively straightforward, though some platform-specific considerations are important.
How to Access and Install Tor
The official and safest way to acquire Tor Browser is by visiting https://www.torproject.org/ and downloading the appropriate bundle for your operating system. Always ensure you download from the official site to avoid malicious copies.
Platform-Specific Considerations
- Tor Browser for Mac: Due to Apple's requirements for web browser apps to use Webkit, Tor on macOS may offer slightly less privacy protection compared to its counterparts on Windows or Chromebook, as it cannot employ the same web engine.
- Tor Browser for iOS: An official Tor Browser app is not available for iOS. However, 'Onion Browser' is a recommended alternative. Be aware that Apple's restrictions mean this browser might not have full control over all network traffic, potentially routing some audio or video through your normal connection.
- Tor Browser for Android: The official Tor Browser app for Android can be installed directly from Google Play. Alternatively, the APK file can be obtained from open-source sites like APK Pure, but users should research the safety of such sources beforehand.
- Tor Browser for Ubuntu/Linux: Installation on Linux distributions like Ubuntu can sometimes be more involved than on other systems. The Tor Project's support site provides detailed instructions and troubleshooting guides.
The 'Tor Expert Bundle' is also available, intended for developers who wish to integrate Tor into their applications across Windows, macOS, GNU/Linux, and Android.
How Tor's Anonymity Works: The Layered Approach
Understanding the mechanics behind Tor's anonymity is key to appreciating its strengths and weaknesses.
The Relay Network Explained
When you initiate a connection through Tor Browser, your data packet is sent through at least three random relay nodes: an entry node, a middle relay node, and an exit node. Each node in the circuit only decrypts enough information to know where to send the data next. The entry node knows your real IP address but not your destination. The middle node knows neither. The exit node knows the destination website but not your real IP address. This intricate process ensures that your identity is obscured from the final destination, and vice versa. Each time you open Tor Browser, you are assigned a unique browsing IP address for that session.
A critical point to remember is that Tor's network is volunteer-run. This means your internet traffic passes through other people's computers. While this decentralised model is a strength, it also presents a vulnerability: anyone can volunteer to be a node. This has led to instances of malicious relays, where bad actors set up nodes to potentially intercept or steal user data, particularly at exit nodes where traffic is unencrypted.
Beyond anonymising user traffic to the clear web, Tor also facilitates 'hidden services', often referred to as .onion sites. These services keep the publisher of the service anonymous, just as Tor keeps the user anonymous. The connection is relayed through multiple nodes on both the user's and the service's side, ensuring mutual anonymity. This is why some refer to Tor as the 'onion browser'.
To access these hidden services, you need their specific .onion domain names. Many well-known organisations, including Facebook and Wikipedia, have .onion counterparts for users seeking enhanced privacy. While search engines like Ahmia can help discover some hidden services, and 'The Hidden Wiki' was once a primary directory, caution is advised. There is no single official Hidden Wiki, and many fake or malicious sites claim to be the real thing, often linking to objectionable or illegal content.
Is Tor Browser Truly Safe? Weighing the Risks
While Tor Browser is an exceptional tool for anonymity, its safety depends heavily on how it's used and the sites visited. Browsing familiar 'clear web' sites through Tor is generally safe. However, venturing into .onion sites requires significant caution.
Legalities and Illicit Activities
Tor itself is not illegal. It is a software tool, much like any other browser. However, much of the activity conducted on the dark web through Tor is illegal. The legality of using Tor, or accessing specific dark web sites, is subject to the laws of each respective country. In some jurisdictions, merely accessing certain dark web content might be deemed illegal. Users must exercise common sense and adhere to local laws. The lack of central regulation on the dark web means it can become a breeding ground for illicit activities and cybercriminals, from black markets to the distribution of illegal materials.
The Advantages of Using Tor Browser
Despite the inherent risks, Tor Browser offers compelling advantages for those seeking enhanced privacy and access.
- Open Source: Tor's source code is freely available for inspection and modification. This transparency means that anyone can scrutinise its operations, ensuring that there are no hidden backdoors or malicious functionalities. This collective oversight fosters trust and accountability.
- Decentralised Server Network: Unlike traditional browsers or even some VPNs, Tor operates on a decentralised network of volunteer-run servers. There is no central authority monitoring or recording user activity, and browsing history or site data is not stored after a session ends. This structure significantly enhances privacy by preventing a single point of data collection or control.
- Multilayered Encryption: As discussed, traffic is encrypted three times and relayed through random servers. This robust, multi-layered encryption makes it incredibly difficult for third parties to intercept or decipher your online communications. However, it's crucial to remember that the exit node does not encrypt traffic, making the final leg of your journey vulnerable if not paired with a VPN.
- Provides Access to .onion Sites and the Dark Web: Tor is the primary gateway to the dark web, offering access to content and services not indexed by conventional search engines. This includes secure communication platforms, academic research archives, and communities discussing controversial topics, as well as the more illicit marketplaces.
The Disadvantages and Dangers of Tor Browser
While powerful, Tor Browser is not without its drawbacks and significant risks.
- Tor Browsing Can Be Slow: The multi-layered encryption and routing through numerous volunteer relays inherently slow down connection speeds. With millions of daily users and a limited number of relays (typically 6,000-10,000), server overload can lead to noticeable delays in browsing.
- Used for Criminal Activity: The anonymity Tor provides, while beneficial for privacy, also attracts cybercriminals. The lack of regulation makes the dark web a hotspot for illegal markets, hacking services, scams, and the distribution of illicit content. Users risk encountering highly objectionable material or falling victim to criminal schemes.
- Risk of Deanonymization: Despite its design for anonymity, Tor is not foolproof. Authorities actively monitor the network, and past incidents, such as the FBI hacking over 8,000 dark web users in 2015, demonstrate that deanonymization is possible. Users can inadvertently reveal personal information, or sophisticated attacks can exploit vulnerabilities to link activity back to a real identity.
- Threat of Malware: The unregulated nature of the dark web means a higher prevalence of malware. Cybercriminals frequently disguise malicious files as legitimate downloads. A notable incident in March 2023 saw thieves stealing approximately $400,000 in cryptocurrency from users who downloaded fake Tor Browsers.
- Less Protection on Certain Systems: While generally secure, specific system configurations can be more vulnerable. JavaScript exploits have historically affected Tor, making Windows users, who form a large part of Tor's user base, particular targets. Apple's restrictions on web engines can also limit Tor's privacy on macOS and iOS. Furthermore, in 2017, Linux and macOS Tor users experienced an IP address leak due to security flaws.
- Hackers Use Exit Nodes: Since anyone can register to be an exit node with minimal regulation, malicious actors can operate these nodes. This allows them to perform 'man-in-the-middle' attacks, intercepting unencrypted data as it leaves the Tor network. Moreover, if any of the three nodes in your circuit (entry, middle, or exit) are compromised, your identity could potentially be pieced together.
Tor vs. VPN: A Critical Comparison
While both Tor and Virtual Private Networks (VPNs) enhance online privacy, they operate differently and offer distinct benefits.
| Feature | Tor Browser | VPN (Virtual Private Network) |
|---|---|---|
| Encryption Layers | Multiple (3+ relays) | Single (via one server) |
| Server Network | Volunteer-run, decentralised | Privately-owned, centralised |
| Primary Purpose | Anonymity (user & destination) | Privacy (hides IP from sites, encrypts traffic) |
| Cost | Free | Generally paid subscription |
| Speed | Often slow due to relays | Typically faster, minimal impact |
| Access to .onion Sites | Yes | No (unless configured with Tor) |
The Power of Pairing Tor with a VPN
For the highest level of privacy and anonymity, combining Tor with a VPN is highly recommended. This setup addresses some of Tor's inherent security holes. By connecting to a VPN *before* launching Tor Browser, your ISP only sees you connecting to the VPN server, not directly to the Tor network. This shields your location from Tor's entry nodes. Furthermore, the VPN encrypts your traffic even after it leaves Tor's exit node, providing end-to-end encryption and protecting your data from potentially malicious exit nodes.
Using a VPN over Tor Browser not only strengthens your online privacy but also prevents your ISP from knowing you are using Tor at all, which can be a significant advantage given the stigma sometimes associated with Tor network usage.
Essential Tips for Safe Tor Browsing
To maximise your safety and privacy when using Tor Browser, consider these crucial tips:
- Enhance Your Security Levels: Tor Browser offers three security settings accessible via the shield icon in the top-right corner:
- Standard: All browser and site features enabled by default.
- Safer: Disables JavaScript and some fonts/math symbols on non-HTTPS sites. HTML5 audio/video and WebGL become click-to-play.
- Safest: Disables JavaScript and some fonts, icons, and math symbols on all sites. HTML5 audio/video and WebGL are click-to-play. This setting provides the highest level of security but may break some website functionality.
- Only Use HTTPS Sites: Always ensure the websites you visit use HTTPS (Hypertext Transfer Protocol Secure). HTTPS encrypts and authenticates information exchanged between your browser and the website, making it significantly more secure than HTTP. Never input personal information on an HTTP site.
- Don't Reveal Personal Information: The core purpose of Tor is anonymity. Voluntarily providing your name, address, email, or phone number defeats this purpose and exposes you to significant risk, especially on the dark web.
- Don't Download Unrecognised Files: The dark web is rife with malware disguised as legitimate files. Be extremely cautious about what you download and from whom. Avoid downloading files from untrustworthy or unknown sources.
- Install Antivirus Software: A robust, up-to-date antivirus solution is an essential layer of defence. Tools like AVG AntiVirus Free offer real-time protection, blocking malicious websites and downloads that might lurk on the web, even if you accidentally click a suspicious link.
- Don't Click Suspicious Links: Many links on the dark web can lead to illegal marketplaces, highly objectionable content, or malicious downloads. Exercise extreme discretion before clicking any unfamiliar or suspicious link.
Frequently Asked Questions About Tor.taxi and Tor Browser
Is tor.taxi genuinely legitimate?
While some external evaluators give tor.taxi a low trust score, indicating caution is needed, users within the Tor community generally consider it legitimate and functional. Its use of I2P links and association with other established dark web entities like Dread (via daunt.link) further supports its operational status within that ecosystem. However, 'legitimate' in this context refers to its operational status, not necessarily its ethical standing or the safety of its environment.
How safe is Tor Browser for general use?
Tor Browser is safe for general 'clear web' browsing if you follow best practices and download it from the official Tor Project website. For navigating .onion sites, safety is significantly reduced due to the unregulated nature of the dark web, increasing exposure to illicit content, scams, and malware. Combining Tor with a trusted VPN enhances safety.
Why is browsing on Tor often slow?
Tor browsing is typically slow due to its multi-layered encryption process, which routes your connection through at least three volunteer-run relays globally. This intricate path takes more time than a direct connection. Additionally, the limited number of relays compared to the large daily user base can lead to network congestion and reduced speeds.
Is using Tor illegal in the UK?
No, using Tor Browser itself is not illegal in the UK. Tor is a privacy tool. However, engaging in illegal activities while using Tor, such as accessing prohibited content, trading illicit goods, or participating in cybercrime, is strictly illegal and subject to the full force of the law.
Can my online activity on Tor be traced?
While Tor is designed for anonymity, it is not completely untraceable. Sophisticated adversaries, particularly state-level actors, may be able to de-anonymise users through various techniques, including traffic analysis, exploiting software vulnerabilities, or compromising Tor relays. Furthermore, users can inadvertently compromise their own anonymity by revealing personal information or downloading malicious files. For enhanced protection, pairing Tor with a VPN is advised.
Uninstalling Tor Browser: A Simple Process
Uninstalling Tor Browser is remarkably straightforward. Unlike many applications, Tor does not typically install itself deeply into your system or make changes to the Windows Registry. It is often a self-contained .exe file. To uninstall, simply delete the Tor Browser folder from your computer and then empty your Recycle Bin. There's no need to worry about leaving residual traces in system programs, as Tor is designed to be fully portable.
Protecting your online privacy and security is paramount in today's digital age. While Tor Browser offers unique capabilities for anonymity and access, understanding its strengths, weaknesses, and how to use it safely is crucial. Tools like AVG Secure VPN can further bolster your online defences, providing military-grade encryption and helping to shield your entire internet connection from prying eyes, whether you're using Tor or simply browsing on public Wi-Fi.
If you want to read more articles similar to Is Tor.taxi Legit? Navigating Dark Web Transport Anonymously, you can visit the Taxis category.

